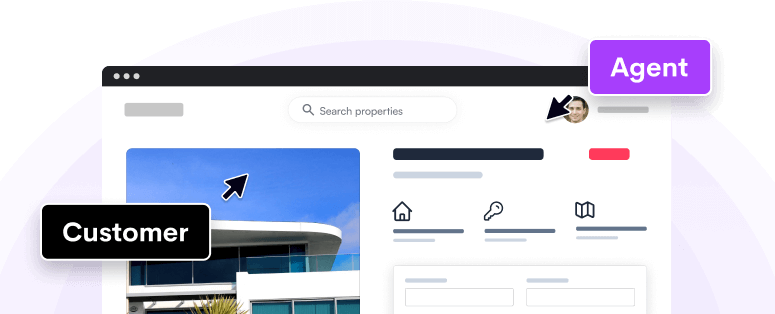
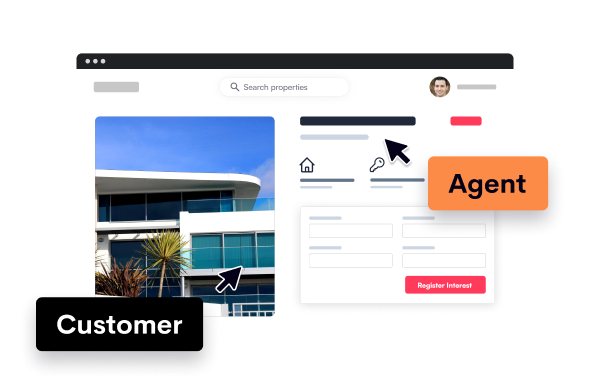
One click to support and sell to even your least tech savvy users
See what your customer sees in one click, draw on their screen to guide them or take control to click for them. Instant, interactive, incredible.
See who loves using next-generation screen sharing
Meet the innovators who've transformed their workflow with Upscope's cutting-edge screen sharing
Join these industry leaders choosing Upscope
Nursegrid, Workable and Figure chose Upscope because of our Speed, Stability, and Security.



Join our customers getting 45% faster onboarding and support sessions
-
"Our data shows Upscope has cut our onboarding team's call time by 27%, which is fantastic."
 Cainen GeretyEX Sales Manager at Square
Cainen GeretyEX Sales Manager at Square -
“Screen sharing is a critical tool in Sungage’s quest to provide remarkable customer service. We were able to install and configure Upscope in just a few minutes.”
 Mike GilesCTO at Sungage Financial
Mike GilesCTO at Sungage Financial -
"We use it on a daily basis and can't imagine doing this work without it! Upscope is a great investment it eliminates guesswork, allows us to keep our customers happy, and saves us lots of time!"
 Tzviatko ChiderovDirector of Merchant Success at Occasion
Tzviatko ChiderovDirector of Merchant Success at Occasion
Discover and Learn
Check out the Upscope blog for more insights on how to communicate better with customers online.